How can we prevent overlay attacks efficiently?
Android market share has now reached almost 75% (source) of the estimated total number of smartphones. Because of this, criminals are now focusing more and more on this platform, profiting also from the weak permission management implemented in Android.
The issue we are trying to address with this product is called "Application Overlay" and permits an attacker to draw on top of any window and application running on the infected device. Firstly malicious applications monitor which applications are started by the user on the infected system. Next, once they detected a sensible application (eBanking, VPN, ...), the malware will redraw an exact login screen on top of the legitimate one. The user is incapable of distinguish the fake from the original and enters the credentials on the wrong dialog. The malware generally upload the stolen credentials to its Command & Control server. To learn more on how this vulnerability works check the articles in the press section.
Overlay attacks are known since 2011 and affect all Android versions up to Android 5.1.0 where the GET_TASKS permission has been made ineffective.
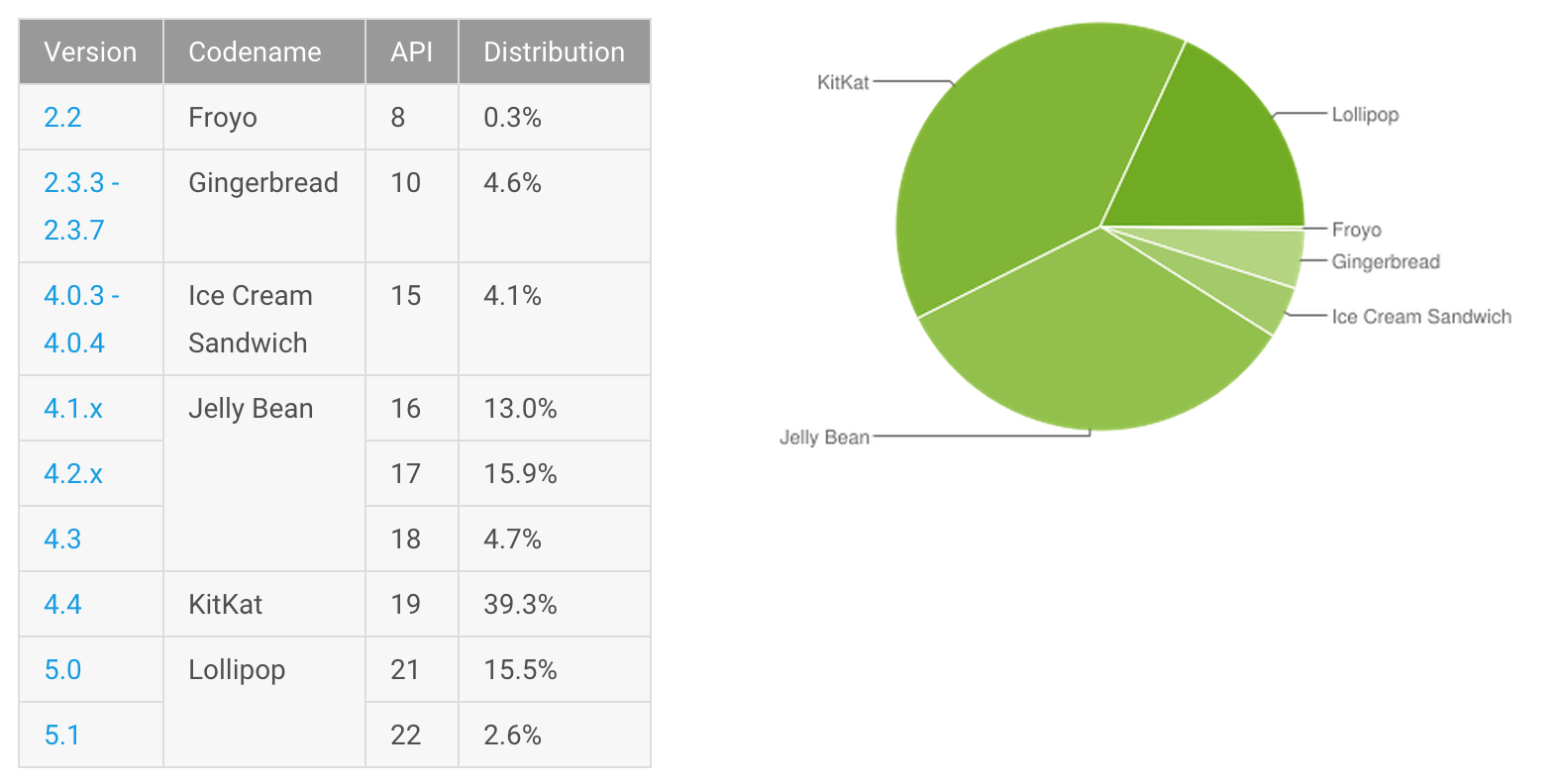
According to the Android distribution of August 2015 shown in the chart below, around 97.4% of devices is affected!
 Nevertheless, cyber attackers found different ways to monitor running process using for example
Nevertheless, cyber attackers found different ways to monitor running process using for example UsageStatsManager, AccessibilityService or by parsing /proc/*/oom_score.
Someone else may just prompt fake view to the user at random time, without monitor the foreground application at all.
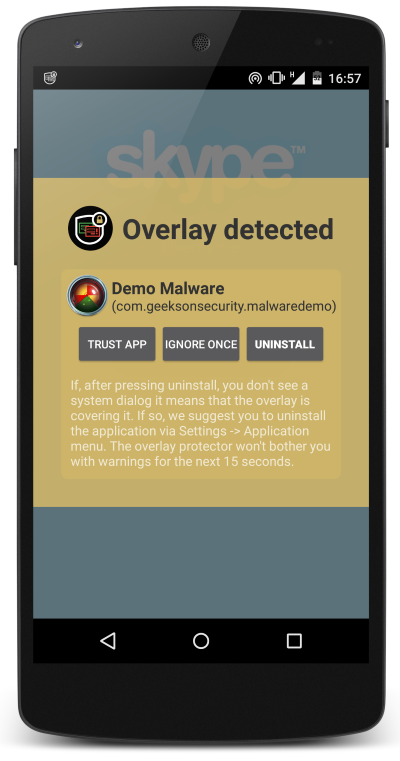
To avoid such attacks, our application constantly monitor every user-interface (UI) change happening on the device. Our detection engine will then check if the view element drawn on the screen is coming from the same package of the legitimate application started by the user. If is not, our application will warn you about it and let you decide if you want to whitelist the potentially malicious application or uninstall it. But careful, not every application which uses this feature want to steal your data. For example, Facebook Messenger application uses this to draw the "chat heads" on top of the screen.
Sneak peaks from the source code
AbstractDetectionEngine and is extended by the following implementation:
BaseDetectionService: For each TYPE_WINDOW_STATE_CHANGED event we perform two different checks:LAUNCH_SINGLE_INSTANCE flag the activity must have a parent, if not raise a warning
_layoutClasses.contains(className) && !isActivity && !parentAvailable, if all of these are met, we raise a warning
AdvancedDetectionService: This engine uses a different approach. We monitor the current process and refresh it at each user tap (TYPE_VIEW_CLICKED) than, for each of the following events: TYPE_WINDOWS_CHANGED, TYPE_WINDOW_CONTENT_CHANGED, TYPE_WINDOW_STATE_CHANGED, we check if the event source match the current process package and, if not, we raise a warning.Settings section of the application.
All the capabilities in one single shot!
Wanna try a not so malicious sample?
To better sensibilize the user about the overlay issue in Android, we created a sample malware which shows what can be achieved by malware authors. The malware sample doesn't steal anything in the end (don't even use the Internet permission) and will only collect the stolen credentials in memory.
You can have a look at the source code yourself since its hosted on GitHub!
How it works?
What this pseudo-malware does is to continuously monitor the foreground process and wait until one known process is started by the user.
With known process is meant a process where the malware has a fake view to inject.
Our malware currently injects to the following applications: LinkedIn, Skype and Credit Suisse Banking.
Install
First you need to download the last APK from the project release page.
If you prefer, you can clone the source and build the package yourself.
Since the package is not coming from Google Play, you need to enable the "Unknown sources" flag in the Security Settings of the device.
This last step is only required if you are deploying to a real device, emulators normally allows install of untrusted apps by default.
To install on a real device, you can issue the following command:
# adb install -r android-overlay-malware-example-X_X.apkor just upload/download it from a cloud storage and install it directly on the phone. You should then find the Demo Malware application in the application list. Per default the malware will try to inject to all supported application, you can change this behaviour by adjusting the settings directly within the application.
See what’s included in the App
Who talks about this vulnerability?